Why Should Higher Education Institutions Adopt Zero Trust?
Higher education institutions are increasingly adopting zero trust, one of the most effective security strategies available to organizations today, but many are still early in their implementations.
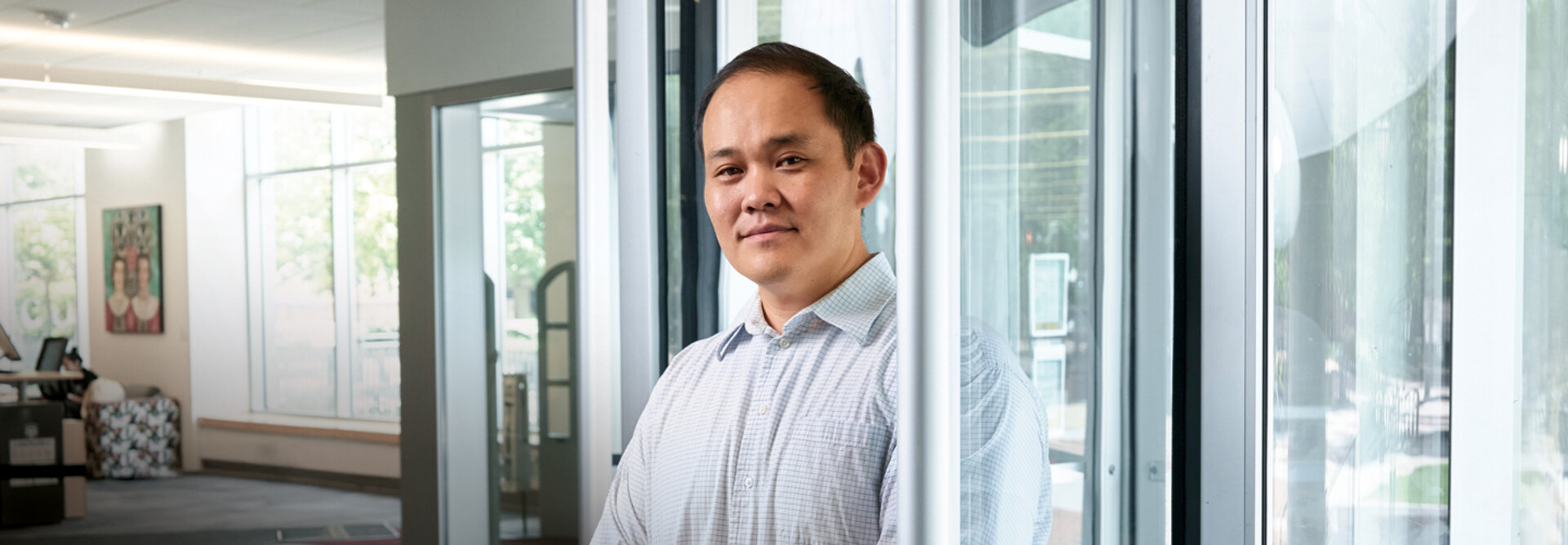
In the past few years, the popularity of zero-trust has exploded into a nearly unanimous agreement that all cybersecurity should be approached in this fashion, says analyst John Grady of Enterprise Strategy Group.
“More are moving down the zero-trust path, but it can be a big, complex undertaking,” he says.
A zero-trust architecture is designed around the principle of “never trust, always verify,” requiring continuous authentication and verification of users and devices to access resources.
Zero trust also enforces least-privilege access, giving users only the minimum access needed for their jobs, and focuses on five pillars: identity, devices, networks, applications and workloads, and data. According to the Cybersecurity and Infrastructure Security Agency, visibility and analytics, automation and orchestration, and governance through policies and procedures are woven through the five pillars.
How Institutions Can Implement Zero-Trust Strategies
Many IT organizations adopt zero trust with targeted projects first instead of diving immediately into comprehensive, organizationwide efforts, Grady says.
Organizations should begin by identifying their most critical security gaps and highest areas of risk, then assess existing technologies that can support zero-trust principles before determining what new tools they need.
Starting with access controls makes sense because it’s typically an area of greatest need, particularly for organizations modernizing remote access following the pandemic, Grady says. Traditional on-premises and remote access methods are fundamentally broken and often represent the most outdated part of the entire technology stack, he says.
“It’s almost indefensible to argue that what we were doing before — with a publicly visible VPN where you had access to everything — worked great,” he says.
VCU’s Han describes it as the traditional castle-and-moat security approach: firewalls protecting everything inside where everything inside is trusted, while VPNs serve as drawbridges for remote access. But VPN gateways are publicly exposed, and once connected they provide broad network access. Cybercriminals that hack in with compromised credentials can then access the network.
DISCOVER: Identity and access management solutions are a crucial pillar of zero trust.
Grady says colleges and universities need to invest in technology to adopt zero trust, such as zero-trust network access (ZTNA), multifactor authentication, tools that enable network microsegmentation, user and entity behavior analytics to detect anomalies, and data loss prevention (DLP).
But zero trust goes beyond technology. Organizations must also create policies that map back to zero-trust principles, such as least privilege and continuous authentication, he says.
“You can put tools in place, but if you don’t write the policies the right way, you don’t have zero trust,” Grady says.
Unlock Exclusive Cybersecurity Insights
Complete the form below to be redirected to CDW's exclusive proprietary research report on Cybersecurity. Once the form is submitted, you’ll be opted into our Security email stream.
Zero-Trust Solutions Can Secure Remote Access
VCU adopted zero trust because the 28,800-student campus in Richmond, Va., had become a borderless organization. With many employees working remotely — some hybrid, some fully remote — the traditional security model was no longer sufficient.
Han had two primary goals: deploy location-agnostic security to ensure consistent protection regardless of user location and enable seamless yet secure access to resources, whether cloud-based or in the data center. The security team also needed continuous visibility into user activity on their devices.
In the office, the IT department safeguarded the network with traditional network security, such as firewalls and intrusion detection systems. But remote employees didn’t get the same level of protection. They had some protections, such as email filtering and endpoint security on laptops, but the security team lost visibility into device activity and user behavior.
To fix that, VCU implemented Zscaler’s ZTNA software to replace its VPNs. The software creates direct, encrypted connections between users and the cloud-based and internal apps they are allowed to access.
All traffic is first routed through Zscaler’s cloud-based security stack, including firewalls and intrusion prevention systems, which prevents users from downloading malware or going to phishing sites, Han says. ZTNA is more secure than VPNs because users only access the specific applications they are authorized to use, rather than gaining broad network access.
To manage application access, VCU used its HR system as the single source of truth, incorporating department IDs and job codes. These parameters allowed Han and his team to configure granular controls over what applications and data each employee could access.
Access provisioning is now fully automated. When users log in to their laptops, Microsoft Entra ID (formerly Azure Active Directory) authenticates them and automatically retrieves their information from the HR system. Entra ID then feeds that data to Zscaler, which grants or restricts access to specific applications based on each person’s role.
A protocol called SCIM (System for Cross-Domain Identity Management) allows VCU’s HR system and security tools to communicate and sync employees’ identity information and access permissions.