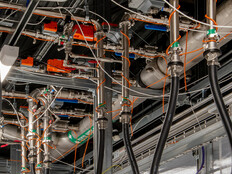
Will Your Configuration Backups Survive an On-Premises Disaster?
Backup data needs to be stored offsite, away from any disaster that might impact your campus. That offsite location should be accessible to anyone who needs access to backups during a disaster recovery.
If the offsite backup is an informal scheme — for example, a thumb drive that a sysadmin takes home — then that person can become a single point of failure during a crisis. A better offsite approach is a solution that backs up to the cloud or other secure remote storage.
MORE ON THE CLOUD: Share these three insights on data protection for your K–12 district.
Who Has Access to the School’s Backup Repository?
Many schools rely on a key staffer or outside consultant for their IT operations — potentially a single point of failure during a disaster. Make sure that a few key people have access to the configuration backups required to bring devices back online.
Don’t overlook training for those key people; if you give the school principal access to configuration backup data, make sure she is able to fulfill that data restoration role should the need arise.
Is Your DR Runbook Current?
Part of a disaster recovery solution is the “runbook” — the book with the processes, documentation and authentication data required to bring a school’s IT system back online. Runbooks tend to be neglected, but as IT systems change, you must update the DR runbook to reflect the current state of the network.
To ensure your runbook is current, schedule a periodic DR drill. For schools, vacation weeks or the summer break are good windows to perform this review and complete the runbook audit.
RELATED: Maximize network health while minimizing classroom disruptions with these tips.
Is Your Backup Repository Secure?
As hackers evolve their attacks, IT management systems have become targets. These systems are tempting because they have privileged access to IT infrastructure such as servers and network devices. If hackers can compromise the management system, they can use it as a springboard into the larger network, gathering intel, creating back doors and installing malware.
IT teams need to periodically audit IT management systems and device configurations to be sure that the bad guys haven’t established a beachhead.
With some extra care paid to your device configuration backups, your school will be positioned to get up and running again should the worst happen.