With its focus on layered security and comprehensive fortification, many refer to defense in depth as a “castle approach” to cybersecurity.
In medieval times, castles often housed hundreds of people — not just kings and lords, but also servants, soldiers, clergy, blacksmiths and countless others, along with their livestock, weapons and other valuables. The more valuable the contents and residents of that castle, the more alluring the site might be to attackers.
With so much area to protect, those charged with designing the castle’s defenses understood that no single measure would suffice to stop an invasion. So, castle defenses depended largely on an interwoven system of protections — the gate, the towers, the moat, the guards — to deter would-be invaders.
MORE ON EDTECH: Learn more about effective incident response.
The same is true of an effective defense-in-depth strategy. No single cybersecurity solution is enough to protect your university’s network or the troves of valuable data inside it. Protecting your data from constantly evolving and increasingly aggressive threats requires a full-stack, defense-in-depth security approach, with your access control, identity management, firewall, anti-virus and other solutions fully integrated and working together.
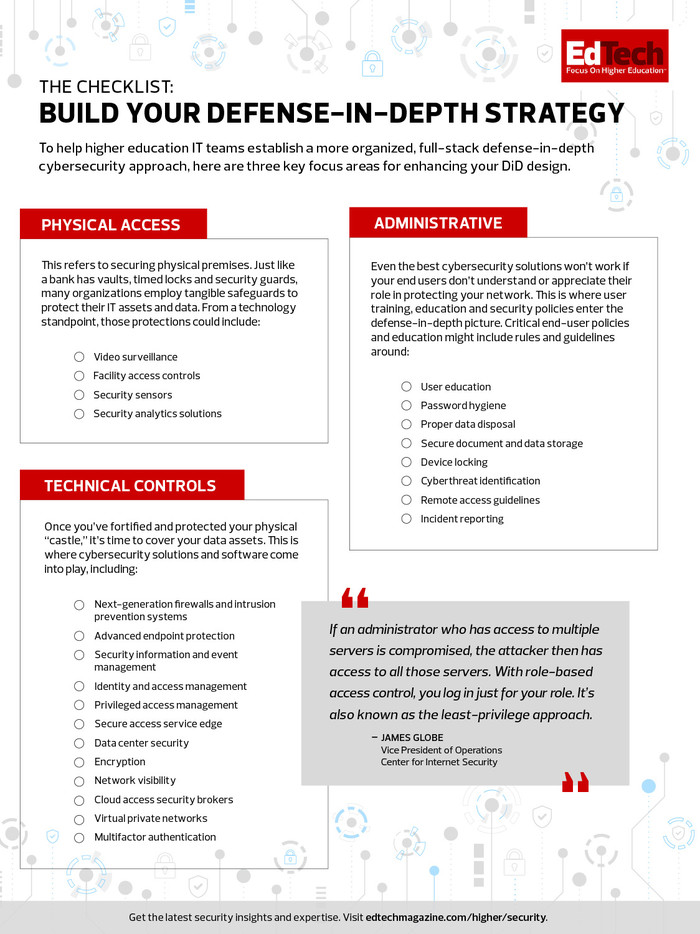
Type the term “defense in depth” into a search engine and you’ll get countless articles attempting to explain what it means and what its most crucial components are. The most agreed-upon definition focuses on three defense categories: physical, technical and administrative.
But what do those categories mean, and what elements are required to protect them? This checklist offers an overview of what you need to build a solid defense-in-depth strategy.
Download the checklist.