Simplified Control Manager Supports Several Capabilities
At the heart of the UCE platform is the MVISION console. It supports several capabilities, including acting as a cloud access security broker, a secure cloud gateway, an endpoint protection platform and a data loss prevention tool. We mostly tested the cloud access capabilities, although the rules we created could also apply to the rest of the infrastructure as well.
The UCE platform was surprisingly easy to manage despite the complexity of the demo environment where it was being tested. As a test, I was able to apply a security policy to any application that used the Mail.ReadBasic scope. Once the new rule was in place, the dashboard showed me how many applications were affected by the new policy. Because the UCE is context aware, I could set up automatic actions based on almost any situation.

Established Access Policies Enhance Security and Collaboration
I could, for example, set one policy for a valid user on a personal device and another for a valid user on a company-owned resource. Some of the many possible actions available included revoking access, forcing users to interact through an isolated browser and forcing a security update to bring a device into compliance.
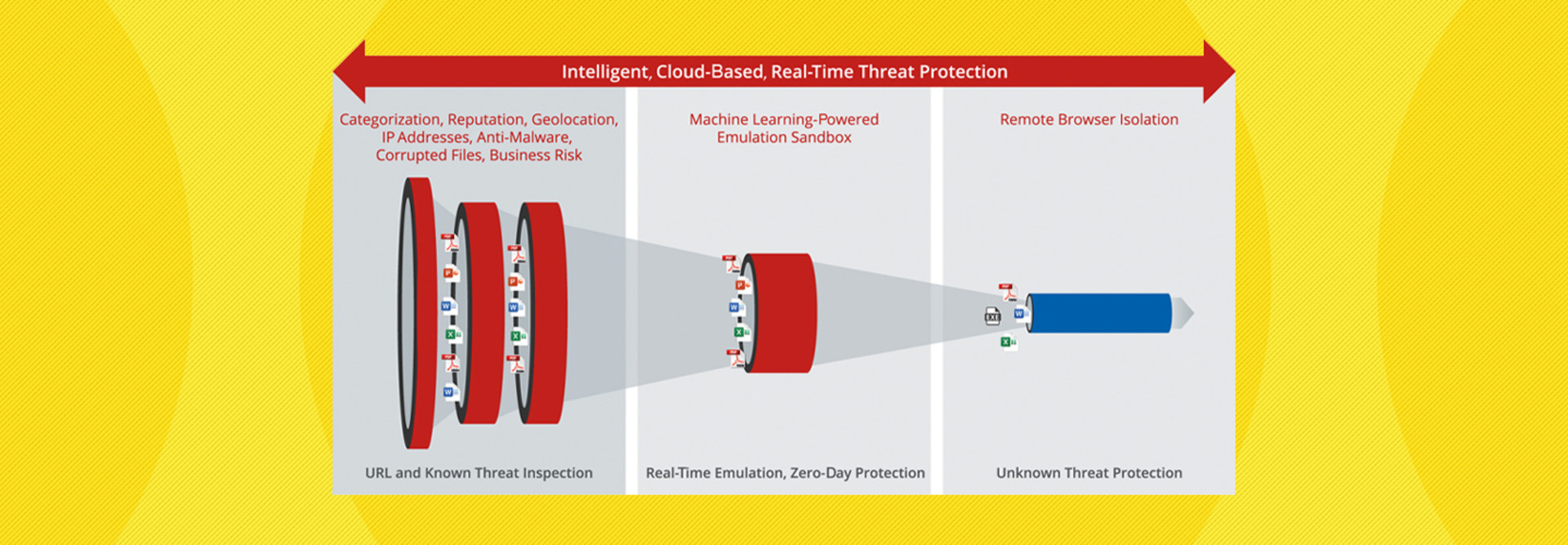
The remarkable thing about the McAfee UCE is that because the entire platform is context aware, and because administrators can finely tune access and permissions based on that context, it provides a bridge to a zero-trust environment. At least for cloud applications, universities can tap the UCE to provide the most robust zero-trust protection possible in today’s increasingly dangerous threat environment.
DISCOVER: Future-proofing higher education's infrastructure security strategy.
Tailoring Access with McAfee MVISION UCE
To test how the McAfee MVISION UCE platform handled various situations, I set up several precise rules for applications, users and processes. In all cases, the UCE handled traffic exactly the way I specified. Whenever it did something incorrect, it was because I didn’t set the rules up just right.
Working with the UCE is fairly straightforward, but since managers are basically configuring a zero-trust environment, it may take a little while to learn all the nuances of what this powerful program can achieve. McAfee can offer training to go with new deployments.
In the first scenario, I had a valid user with all correct passwords attempt to access a simulated network on a personal device. Per our policy, the user was given full access to the network but was prevented from downloading or uploading any files since a personal device not controlled by the entity was being used.
A second user was also valid and working on an organization-owned asset. However, the security patches were not up to date, so the device was noncompliant with my security policy. In this case, the UCE gave the user the choice of interacting with the site using browser isolation (so it could not actually affect the network) or applying all the patches and then, after the UCE verified that they were again compliant, accessing everything normally. It’s worth noting that assets owned by the organization need to have a UCE agent running on them to verify policies and provide better monitoring.
LEARN MORE: A proactive approach to avoiding zero-day attacks in higher education.
Yet another valid user with an organization-owned device had active malware on the system. The user was denied access to the network and had future access revoked until a human administrator could verify that it was safe for the user to return.
In addition to managing users, McAfee UCE can also enforce rules regarding how cloud-based applications communicate with one another, or what happens when a previously unknown application tries to access network resources.
Managing everything about cloud deployments, data and access from a single program is easily possible through the UCE. In every scenario tested, the UCE performed exactly as requested. This eliminated many vulnerabilities in the cloud-based test bed, ensured they stayed away and enabled total control of an entire cloud infrastructure from a single, user-friendly console.
Specifications
Technology: Cloud-based security software
Cloud Platforms: Amazon Web Services, Google Cloud, Microsoft Azure and many others
License Type: Annually per user
Maximum Users: Unlimited
Technical Support: Available 24/7