Best Practices for Cybersecurity Are Simple and Keep Users in Mind
As students, faculty and staff settle into the routines of a new semester, it’s the perfect time for a refresher on cybersecurity. Perhaps this is why October is designated National Cybersecurity Awareness Month. CIOs and CISOs have an opportunity to educate users on the basics of good cyberhygiene before they develop bad habits.
The Department of Homeland Security recently released its themes for October, from basic online safety to cybersecurity careers. Each week, DHS and its partners will release resources relating to each theme that IT staff can incorporate into cybersecurity education and training.
These resources, paired with best practices from other institutions, can help IT leaders ensure that end users stay safe online.
SIGN UP: Get more news from the EdTech newsletter in your inbox every two weeks!
Start with Basic Cyberhygiene
According to the Digital Citizens Alliance, nearly 14 million higher education credentials are on the dark web. That makes it even more critical to keep login information safe from hackers.
The easiest way to do so is to practice secure password habits. The Digital Citizens Alliance recommends:
- Use a mix of characters.
- Make the password as long as is allowed.
- Do not reuse university-provided passwords.
- Change passwords annually or whenever exposure is suspected.
- Never share your password.
Recommending best practices is one thing. Getting users to actually follow them is another. If IT leaders want users to change their passwords regularly, or at least update them from the default password, they need to make it easy. Multifactor authentication and, where feasible, thumbprint recognition are great user-friendly security measures.
Another basic tenet of good cyberhygiene is knowing how to thwart phishing. Today’s phishers have gotten more sophisticated than the Nigerian prince scammers of years past. Fraudulent emails now appear more official and are tailored for specific users at specific times. Ongoing education is important to alert users to current scams and remind them how to identify suspicious emails, such as hovering over a link to determine the destination URL.
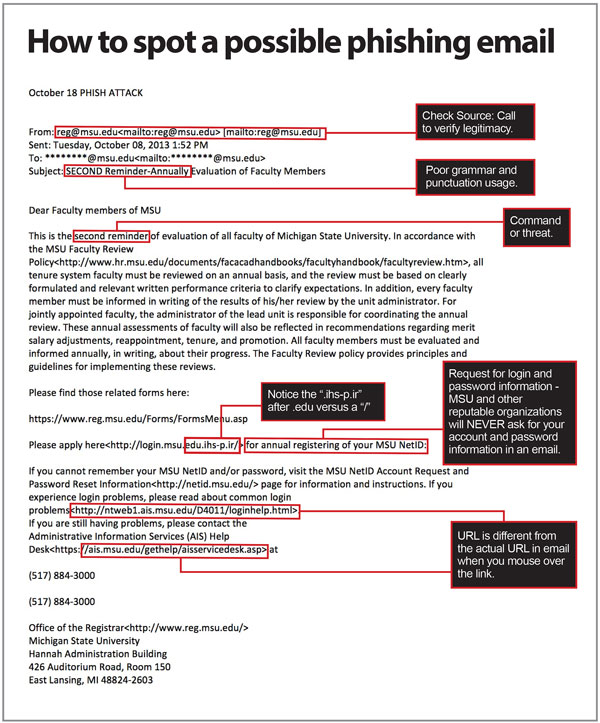
SOURCE: Michigan State University's SecureIT
For example, some institutions send campus users a detailed list of the information that they would and would not ask for via email. Others step up their education campaigns during high-cybercrime periods, such as tax season, to keep staff and students wary.
Establish Good Security Habits
The best way to enlist users’ support in security — and perhaps the most difficult — is to reinforce good habits. One great strategy is to teach users how to protect their data at home and on their personal devices, with the aim of encouraging them to carry those strategies over to the workplace.
This tactic also takes into account the reality that the line between home and work is increasingly blurred. Users connect personal devices to campus networks, and they access institutional documents at home and in public places (such as coffee shops), whether on personal devices or those owned by the institution. Accordingly, it’s a win-win to teach users to be secure in their personal lives.
Another simple strategy is to encourage faculty and students to use a virtual private network, a tool that lets them access work anywhere while keeping networks safe. Here again, as with password maintenance, IT staff need to make sure that VPNs are user-friendly. If it’s easier for a student or faculty member to circumvent security to get their work done, they’ll do so. But if the most secure option is also the easiest, everyone will be safer.
For more higher ed security best practices, check out this video from CDW.
This article is part of EdTech: Focus on Higher Education’s UniversITy blog series.












