Bring Shadow IT Out of the Dark
CISOs know they will always have to deal with shadow IT, those hidden pockets of technology that users obtain and implement outside of official channels. Arguably, it’s the nature of a college environment that students, faculty and staff will continuously push the edge with new tools.
For many institutions, cloud computing is an effective, speedy way to provision productivity applications. But when departments sign on with cloud providers before IT can test or approve their services, these uses fall into the realm of shadow IT.
Understandably, that makes IT teams nervous: If they can’t test a product or they aren’t even aware that it exists, the potential for a security breach increases.
Between these two poles is an effort to bring shadow IT into the light, to ensure that users’ technology needs are met and that institutions can deploy a broad range of cloud applications securely.
Facilitating an IT Culture Change
At the University of Michigan, the IT department has certified the use of Box to store medical data that falls under Health Insurance Portability and Accountability Act regulations, a move that also makes it easier for campus researchers to share their data.
“By using Box, the university has stopped people from sending sensitive information over email or sharing it with unencrypted USB drives,” says CISO Donald Welch.
And at The Ohio State University, CISO Helen Patton says the university now requires a security assessment anytime a college or unit wants to put restricted data in the cloud.
“This process is very mature, and it’s creating the right kind of security engagement at the university,” Patton says. “Cloud services have included online testing, electronic lab notebooks, survey tools and others — all being used across Ohio State University.”
According to security consultant Cheryl Biswas, one factor that can minimize shadow IT is a culture in which staff members don’t perceive the IT department as a bottleneck.
“Both sides have to make compromises,” she says, affirming the importance of official channels when it comes to approving new tools. “It may slow down the pace of innovation somewhat, but given the risks of a breach, it’s much more important for the product to be deployed safely.”
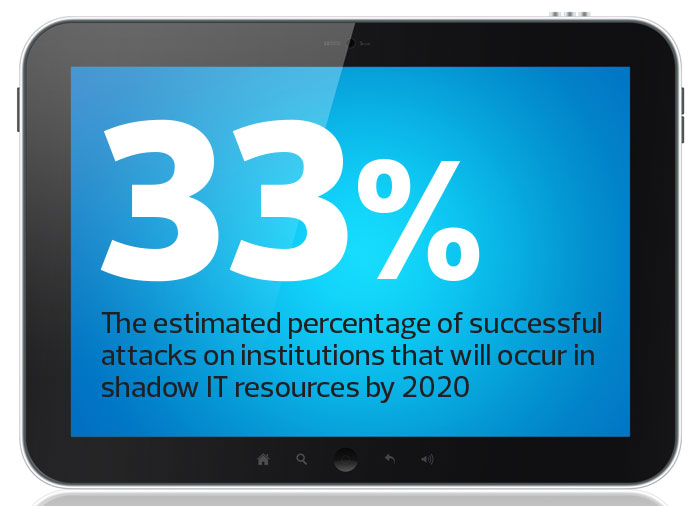
SOURCE: Gartner, “Top 10 Security Predictions 2016,” June 2016
Best Practices for Guided Choices
The following strategies can help IT teams keep the cloud as a force of innovation on campus, rather than a cause for concern.
Encourage communication: Too often, staff and faculty view the IT department as an obstacle. People may hesitate to work with IT because they fear the department will say no to their ideas. That means IT teams must keep communication open. They can encourage faculty and staff who are interested in Software as a Service applications to work with IT to ensure their plans meet institutional security policies. Users also need to understand that although they may derive short-term benefits from SaaS applications, the risks of a data breach or damage to institutional reputation are far larger.
Identify acceptable SaaS and other cloud applications: The government’s Federal Risk and Authorization Management Program (FedRAMP) reviews cloud products and services for adherence to security best practices and puts “all-clear” vendors on an approved list. To guide faculty and staff toward such vendors, IT can refer them to FedRAMP or create a modified internal list. Whichever path a college pursues, it needs a way to communicate approved vendors to potential users and to request that users work only with them. Such a system gives users the autonomy to choose their own tools within certain parameters.
Encourage users not to run sensitive data over shadow IT: It’s critical that organizations evaluate the types of data they have and how it is being used. Ask users to determine whether they can afford to lose their data and what risks the institution could face if data were lost or stolen. Classified research data from the Defense Department, for example, should not be run over shadow IT.
Think carefully about the most sensitive research: Many institutions struggle with how to secure confidential research data. It’s bad enough when personally identifiable information, such as students’ medical records or Social Security numbers, are compromised. But what about intellectual property pertaining to research on new drugs or autonomous cars? Institutions need to ensure such data does not run on shadow IT and, if any part does run in the cloud, that researchers work only with approved vendors.
Understand the data lifecycle: When applications run over shadow IT, the risk rises that unauthorized people could access institutional data. However a college establishes its cloud contracts, least privileged access should be the standard procedure: Only those who require access to data or applications should have access — and only at the appropriate levels.
According to Biswas, high-profile data breaches have increased public awareness of information security risks. As a result, she says, they are more likely to understand the concerns of CISOs and IT departments, and that creates a better climate for cooperation.
“Start by sitting down and reviewing what each department does with its data,” Biswas says. “Talk about what each stakeholder does, who needs access and what each person in the chain does with the data. Remember that you are asking somebody to change, but they have to understand that the cost of not considering security is a data breach. Once the university loses employee data on the dark web, it’s lost forever.”











