The Basics of Smart Contracts with Cloud Vendors
At colleges and universities worldwide, the adoption of cloud computing is fully under way.
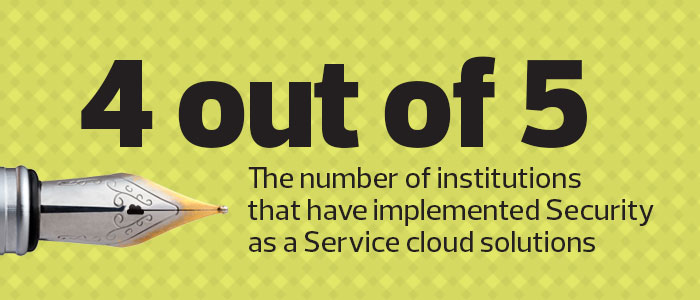
Although the institutions that are pursuing aggressive, “all-in” cloud-first strategies are grabbing the headlines, it’s hard to find any institution that doesn’t have at least one major computing service offered through a cloud provider. Between email and calendaring services, human resources systems and credit card processing, cloud service providers have quickly become an important part of the campus technology landscape.
As institutions move sensitive information and services to the cloud, IT teams must ensure that providers’ security controls are sufficient to safeguard the confidentiality, integrity and availability of the institution’s information assets. Institutions can and do depend on vendors to provide services in a secure manner.
Yet a handshake agreement simply isn’t good enough. When it comes to information security, the stakes are high, and institutions should acknowledge this by incorporating security issues into cloud service contracts. Although vendors typically propose contracts that protect their own interests, institutions must respond by insisting on language that covers key security considerations and provides clear consequences in the event that a provider fails to fulfill those responsibilities.
SOURCE: EDUCAUSE, “Top 10 IT Issues 2016,” January 2016
Assess Risk First
As with many other security activities, institutions benefit by starting the cloud service contracting process with a risk assessment. The goal is to identify the institution’s potential exposure in the event of a security incident.
Does the cloud provider handle sensitive personal information that could result in identity theft? Will a failure of the provider’s services or a loss of information prevent the institution from achieving its teaching, research or service missions? If a breach occurred at the provider, what impact could that have on the institution’s reputation?
The answers to these questions will help determine the nature and rigor of needed security controls. For example, a provider that will handle student credit card transactions should receive much greater scrutiny than one that will host a static website for an academic department.
Negotiate the Fine Points
With the risk assessment in hand, an institution’s security professionals can develop a checklist of the critical controls required to protect the institution’s interests. This checklist serves as a great starting point for conversations and negotiations with the vendor. Security professionals can work their way through the list, asking vendors to describe the way they achieve each control objective and determining whether the measures are satisfactory.
If the provider’s controls are insufficient, the institution has three possible courses of action. First, it can negotiate with the provider to add additional controls that meet the objective. Second, it can introduce its own compensating controls that achieve the same objective, such as encrypting data before it gets to the cloud provider. Finally, the institution can modify the intended scope of use to render the control unnecessary, such as not using the provider for highly sensitive information.
Reinforce with a Contract
The contract between an institution and a cloud provider serves as an important guidepost for the entire relationship between the two organizations. In addition to laying out the services the vendor will provide, the financial relationship between the organizations, and the consequences of a service failure, cloud contracts must also cover many important security issues. Chief among these, the contract should require that the cloud provider continuously maintain the security controls discussed during the risk assessment, and change them only after providing adequate notice to the institution. Some institutions achieve this by including the description of controls as an appendix to the contract.
In addition to requiring the presence of controls, contract language should give the institution the right to audit a vendor’s continued compliance with those controls. This may include the right of institution representatives to physically inspect data centers and conduct security assessments. More commonly, the contract might require that the provider hire an independent assessment firm to conduct a thorough security audit on an annual basis, and then provide the institution with a copy of that assessment report.
Protect All the Assets
Higher education is a knowledge industry, and colleges and universities vigorously protect their intellectual property. IT professionals should work closely with the institution’s attorneys to analyze any intellectual property ramifications of cloud service contracts, particularly when the vendor is offering the service without charge. Contracts may contain buried clauses that transfer ownership of information to the provider or grant the provider a license to use that information in some way. Such provisions could have a significant, negative impact on the institution.
Finally, while security pros who work on cloud contracts should make every effort to develop controls that prevent data breaches, the contract must acknowledge that a breach may occur in the future. Institutions should include language requiring the vendor to promptly notify the institution of a breach and to keep the institution informed throughout the resolution process. The contract may also include provisions requiring the vendor to assume financial responsibility for notifying faculty, staff, students and other constituents, and providing them with credit monitoring services.
A contract that clearly spells out security responsibilities should cover every cloud service that an institution uses. The initial language that vendors propose often contains fairly weak security provisions. Colleges and universities must treat these drafts as the starting point for a negotiating process that seeks to protect institutional interests. The decisions that security professionals and attorneys make during contract negotiation may become extremely important years later, in the wake of a security incident.











