Sneak Attack: Protect Networked Printers Against Unwanted Intruders
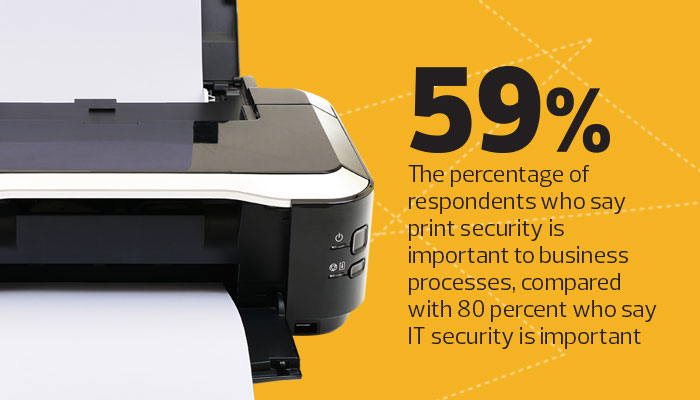
With security concerns surrounding so many technologies, it is easy to overlook printers as a potential source of data breaches. Yet a November 2015 survey by market research and analysis firm IDC found that more than half of the companies surveyed had experienced at least one printer-related breach in the previous year. What’s more, the survey suggests that many organizations could do a better job of keeping printer security on their radar.
Printers at colleges receive, process, store and print extensive sensitive data, from intellectual property to personally identifiable information. Accordingly, they present a golden opportunity for attackers to commit data breaches, achieve financial gain or bring about reputational damage. In addition, networked printers can be a gateway to an institution’s entire system.
Certain threats to confidentiality are strictly local; for example, someone stealing an unattended printout or gaining access to a printer’s storage media to harvest sensitive data. But most threats can be local or remote.
Many attackers use malware, printer attack tools or other methods to compromise printers through network connections. Once a hacker succeeds, that breach can be leveraged for many purposes. The most common aims are gaining unauthorized access to any information being sent to that printer, and using the printer as a starting point to infiltrate other institutional systems.
Given these risks, institutions should take stock of printer-related concerns and develop a realistic plan to address them.
Take Advantage of Features in Newer Printers
New models offer a suite of security features that institutions can deploy for quick, inexpensive security gains.
-
Automatic updates: It’s important that printers use the latest updates for their BIOS, firmware, operating systems and all other installed software. This prevents vulnerabilities and may add new features to boost security.
-
Storage encryption: If a printer’s storage is strongly encrypted, attackers will be unable to recover data even if they gain physical access to the storage.
-
BIOS protection: Some printers check their BIOS every time they boot and can, if they detect unauthorized changes, replace the BIOS with a known good copy. This eradicates malware from the BIOS automatically.
-
Firmware integrity monitoring: A printer that monitors the integrity of its firmware can detect unauthorized changes to the firmware itself, as well as associated issues in the printer’s memory, and force a reboot to clear these from the printer.
-
Authentication: Authenticating individuals whenever they want to use a printer is unfeasible, but it is strongly recommended for printer administrators, who can be authenticated through smart cards, biometrics, PINs or other means. No matter what method institutions use, it’s critically important to change all default passwords or PINs so attackers can’t readily guess them.
-
Storage sanitizing: Some printers have the ability to sanitize storage on demand to prevent it from recovering sensitive information. This is a key step to perform before allowing a printer to leave the institution. Even if a printer uses storage encryption, sanitizing is still recommended because flaws in the storage encryption mechanisms could be detected in the future.
SOURCE: IDC, “The Business Value of Printer Security,” November 2015
Address or Accept the Security Deficiencies of Older Printers
Although many older printers lack the most current security features, these printers have comparatively fewer vulnerabilities, which can offset this deficiency. For example, a particularly old printer might not have any storage. Because there is so much variability among printer models in terms of their vulnerabilities, the severity of these weaknesses, and how they can be addressed, it may be necessary to separately assess the risk for each printer model.
IT administrators usually can’t add technical security controls to older printers, so they may need to choose the best alternative course of action: add manual procedures to reduce risks to an acceptable level; replace older printers; or accept the risks and change nothing. Given the potential cost of a data breach stemming from a compromised printer and the labor involved in manually securing a fleet of printers, replacing older machines is often the most cost-effective strategy.
Balance Availability with Security
Institutions want to ensure students, faculty, staff and guests can utilize their printing services. Increasingly, this means allowing printing from any type of device and any network location. Some institutions allow students to print from mobile devices on cellular networks and from cloud-based services and applications. Unfortunately, this degree of availability can make printers readily accessible to remote attackers, greatly increasing the risk of compromise and misuse.
Most printer vendors don’t intend for their products to be publicly accessible. Whenever possible, printers should be behind firewalls that prevent or restrict direct access. If an institution wants a printer to truly be available to anyone, then it’s important to develop plans for dealing with any potential consequences that may arise.
For example, in March 2016, a white supremacist used a simple search to find publicly accessible printers, including a dozen at various universities, and remotely printed anti-Semitic materials at those institutions. Such incidents could happen at any time, so it’s prudent to, at a minimum, enable auditing capabilities that indicate the sender’s IP address for any such materials.
Risks related to networked printers can be easy to overlook, but they are also among the easiest loopholes to plug, given the proper tools and procedures.